The series of deadly explosions of devices owned by Hezbollah members this week has raised some questions about whether the average smartphone owner should be concerned that their device could also be remotely set to explode.
But security experts are downplaying the potential threat posed by such devices, saying it’s highly improbable that the average person’s phone is at risk of exploding like the pagers and walkie-talkies that blew up in Lebanon this week, killing dozens and wounding around 3,000.
“The concern is understandable and it’s technically possible, but it’s generally unlikely,” said Hadis Karimipour, Canada Research Chair in secure and resilient cyber-physical systems at the University of Calgary.
She and other security experts say it’s important to note that outside agents had gained physical access to the pagers and modified them before they exploded.
Although Israel has neither confirmed or denied its involvement in the explosions, it is widely believed that intelligence officials from the country were responsible for the attacks.
It is believed the devices may have been intercepted at some point in the manufacturing supply chain, where an explosive was inserted, along with some kind of trigger mechanism. Or, as was reported by the New York Times, the devices were manufactured by a front company.
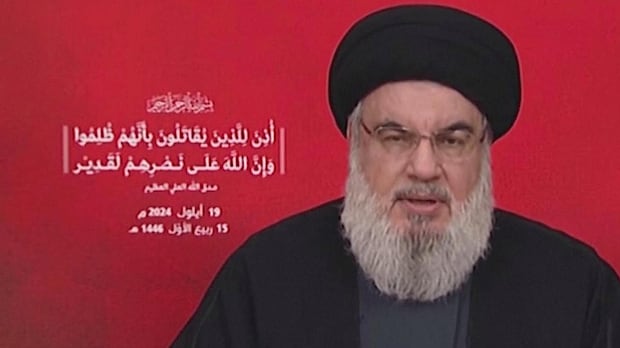
Hezbollah leader Hassan Nasrallah accused Israel on Thursday of targeting thousands of pagers in a wave of attacks that hit Lebanon this week. Israel has neither confirmed nor denied its involvement in the explosions.
Major brands have strong security
Either way, Karimpour says, “that’s something that needs a high level of sophistication and intention,” and she notes that it’s “not something that can happen” during the regular smartphone manufacturing process.
For a smartphone to be similarly compromised, Karimipour says, it would require access to the phones at the hardware level within the manufacturing chain.
She says it’s “very, very difficult” to get access to this process with major brands because of the level of quality control.

Difficult to add explosives to phones
Josep Jornet, a professor of electrical and computer engineering at Northeastern University and the associate director of the school’s Institute for the Wireless Internet of Things, says it’s also important to note that the technology used in pagers is very old.
If you opened an old electronic device, for example, Jornet says you’d be able to see most of the components and potentially add something by hand.
But with a smartphone, he says just opening it can be a challenge as it’s sealed to be waterproof. However, once opened, you’d find many black chips, or integrated circuits on a piece of silicon.
“It’s very hard to to do something to a phone at that level with your hands without someone noticing,” he said. “So it’s going to be very difficult to add explosives to your phones.”
After a second wave of deadly explosions in Lebanon, experts are now analyzing how attackers were able to penetrate Hezbollah’s security to rig thousands of pagers and other devices with explosives.
However, Jornet did say that it would be possible for highly skilled individuals to take control of your phone remotely, whether or not there’s an explosive inside.
Once they have control, they may be able to send unwanted images and messages from your phone or wipe it clean, Jornet says, but that doesn’t mean they could make the device explode, unless they had already physically manipulated it.
“Even if you say, ‘But maybe they can do something so it overheats.’ All the phones today have failsafes that even if they get really hot, they will just switch off.”
Phone supply chains more secure
Richard Forno, assistant director of the University of Maryland, Baltimore County’s Center for Cybersecurity, suggested people can trust that their smartphones haven’t been tampered with because the supply chains and manufacturing processes for them are much more secure.
For example, he says Apple doesn’t give a contract out to just any company in China. According to Forno, Apple would require these companies to have due diligence, proper security, employee vetting and a host of other measures.
“Apple actively monitors every step of the manufacturing process, which includes randomly testing what comes off the assembly line,” Forno said.

He noted that for those in the West, the security of the supply chain is not a huge concern. However, if someone buys a phone from a back-end dealer off a shady website, he says it would be difficult to know where they’re sourcing their materials from.
“That might be a cause for concern. For the average person, their iPhone, their Pixel phone, I have faith in the supply chain overseen by Google and Apple.”
How to protect your phone
Still, Karimipour says that despite the low probability of our phones becoming dangerous explosive devices, there are actions people can take to ensure smartphones won’t be compromised.
Most importantly, she says, people need to stick with established manufacturers and trusted retailers.
“Generally, trusted companies have better quality control and it’s more likely to detect if there is any tampering.”
She says it’s also important to regularly update the software on your phone and to use security features like multi-factor authentication, where users must provide a password and additional identity verification like a fingerprint, to gain access to their device or accounts.
Taking these basic security steps makes it more difficult for outside actors to gain remote access to your devices, she says, noting that it’s also important to keep your phone in a secure place and take good care of it so that “no one can physically manipulate it or remove the battery.”